What is Log Analytics ?
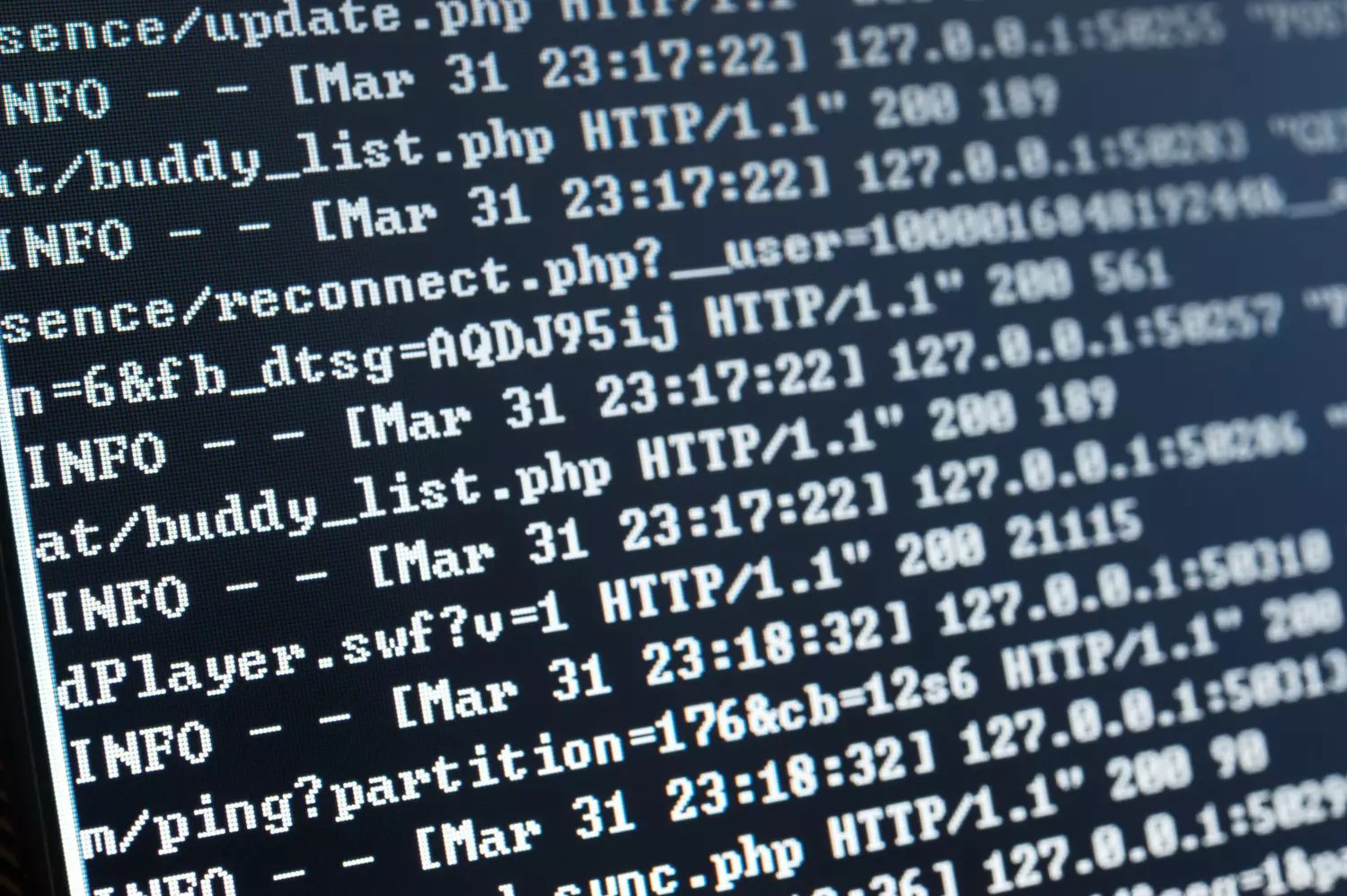
According to Tech Target : “Log analytics is the assessment of a recorded set of information from one or more events, captured from a computer, network, application operating system (OS) or other IT ecosystem component. An organization can use log analytics to uncover patterns in user behaviors, identify problems, audit security activities or ensure compliance with established rules, and plan for capacity or IT infrastructure changes.”
According to NIST Log Analysis is “Studying log entries to identify events of interest or suppress log entries for insignificant events.”
In general, then, we can say that log analysis is the practice of analyzing and interpreting log data generated by computer systems, applications, networks and various other sources.
Why is important to analyse your log ?
The complexity and exponential multiplication of systems has led to an explosion in the amount of logs produced by the software and machines used by a company. To illustrate this explosion, in 2010 the world was producing about 1.2 zettabytes (1.2 trillion gigabytes) of data per year. By 2020, that figure had risen to 59 zettabytes per year. IDC predicts that by 2025, we will be producing 175 zettabytes of data per day.
In this context, analyzing logs has become essential for various aspects of operations and systems management. It helps organizations improve cybersecurity, gain insights into operational processes, optimize system performance, detect anomalies, and enhance overall reliability.
Logs are a valuable source of information that contributes to efficient decision-making in the digital era.
How to perform Log Analysis ?
Below are the three key steps of log analysis. In the second part of the article, you will find Trout Software's approach to streamline this process.
.jpg?width=1462&height=483&name=how-to-perform-log-analysis.JPG%20(1).jpg)
1 / Collect and centralize data
The first step in log analysis is to collect and centralize your log data.
This involves gathering logs from various sources such as servers, applications, network devices, and security systems. Implement a log collection mechanism that captures logs in real-time or scheduled intervals and store them in a centralized location or log management system.
Centralizing logs can pose numerous challenges, including storage quantity and budget constraints. However, Trout Software has adopted a different approach to address these challenges, detailed below 🎣
2 / Analyze your data
Once your log data is collected and centralized, the next step is to analyze it.
There are several approaches to log analysis, including manual inspection, using log analysis tools, or employing machine learning and data mining techniques. Start by defining your analysis goals and questions you want to answer.
Then, apply various analysis techniques such as searching, filtering, aggregating, and correlating logs to extract valuable insights. Look for patterns, anomalies, errors, performance issues, or security breaches that can provide useful information about your systems and applications.
3 / Set up controls to have a fine monitoring of your infrastructure
To enhance your log analysis process, it's crucial to set up controls for fine monitoring of your infrastructure.
This involves configuring alerts and notifications based on predefined thresholds or patterns identified during log analysis. These controls can help you proactively detect and respond to critical events, performance degradation, or security incidents.
Additionally, establish log retention policies to ensure you retain the necessary log data for compliance, troubleshooting, or historical analysis purposes.
What are the benefits of Log Analytics :
Streamlined Troubleshooting :
Log analytics provides a comprehensive view of system activities and events, making troubleshooting more efficient. By quickly pinpointing the root causes of errors, failures, or security incidents, you can expedite issue resolution and minimize operational disruptions.
Strengthened Security Monitoring :
Protect your organization with robust security monitoring. Log analytics allows you to analyze logs for suspicious activities, unauthorized access attempts, or abnormal behavior. By promptly detecting and responding to security threats, you can strengthen your defenses and safeguard sensitive data.
Optimized Performance :
Achieve peak performance with log analytics. By analyzing logs, you can identify performance bottlenecks, resource utilization issues, and configuration errors. Armed with this information, you can fine-tune your systems, allocate resources effectively, and ensure optimal performance.
Compliance and Audit Support :
Simplify compliance reporting and auditing processes with log analytics. By carefully analyzing logs, you can track and monitor system activities, keep comprehensive audit trails, and demonstrate compliance with regulatory standards. This inspires confidence in stakeholders and ensures transparency.
Data-Driven Decision Making :
Log analytics reveals trends, usage patterns, and user behaviors, empowering you to identify business opportunities, streamline processes, and enhance customer experiences.
What challenges does log analysis present ?
.jpg?width=1430&height=589&name=challenges%20of%20log%20analytics.JPG%20(1).jpg)
Variety and complexity of data :
Logs can come in different formats and structures, making it difficult to extract meaningful information. Managing the various sources of logs and their different formats requires data normalization and transformation to ensure consistent analysis. In addition, logs often contain technical jargon, abbreviations, or cryptic error messages, making them difficult to interpret.
Data quality and noise :
Log data can be noisy and contain irrelevant or redundant information that can hinder analysis. Poorly structured logs or incomplete data can impact the accuracy and efficiency of log analysis, requiring data cleaning and filtering techniques.
Scalability and Performance :
As log volumes increase, ensuring scalability and performance becomes critical. Analyzing large-scale log data in real-time or near real-time can be resource intensive, requiring a robust infrastructure and distributed processing capabilities to handle the workload.
Security and Privacy Concerns :
Logs may contain sensitive information, including user IDs, IP addresses, or personal data. Safeguarding connection data and complying with privacy regulations are critical challenges for connection analysis, requiring appropriate access controls, encryption and data anonymization techniques.
Integration and interoperability :
Organizations may have various systems and applications generating logs in different formats and locations. Integrating and correlating logs from multiple sources, interoperating between different log management tools, and centralizing log data for analysis can be challenging.
Trout Software, the emerging log analytics solution ! 🎣
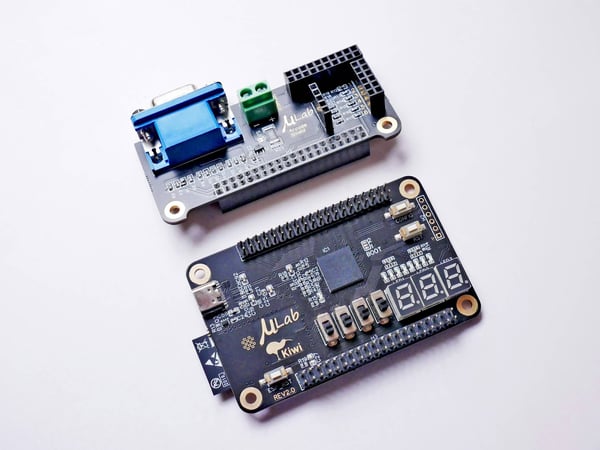
Easy Connection to your logs
One of the challenges of log analysis is accessing all the system logs you want to analyze. To make this easier, Trout Software has developed a set of pre-built connectors that allow you to connect to your data, wherever it is, in just a few minutes.
.jpg?width=1920&height=1080&name=connect-quickly-to-your-datasource%20(6).jpg)
The software allows you to query all these datasources without preliminary ingestion, allowing you to save lots of resources not building ingestion pipelines.
Perform quick log analysis through our no-code interface
Once your data is available, you can carry out your analysis. To do this, open a playbook, connect the desired data sources, and begin your work. After gaining an overview of your data, you can use our no-code interface to perform quick analyses of your logs. The interface includes all the functions described in the photo below.
To add extra context about your environment, you can also drag and drop a CSV, text, log files to add it to your analysis.
.jpg?width=1920&height=1080&name=perform-quick-log-analysis%20(2).jpg)
Automate a control in 3 clicks
If you want to automate a control after analyzing your logs, you can do it in less than a minute with our Scheduler.
Just select the playbook you created (1), configure the control parameters (2), and click on Schedule (3).
.jpg?width=1920&height=1080&name=automate%20playbooks%20dashboard%20(1).jpg)
Conclusion :
In the digital age, log analytics has become an indispensable tool that helps bolster security, operations, ensure compliance, and empower data-driven decision-making. However, it is not without its challenges. Handling diverse data formats and ensuring scalability and privacy are real hurdles.
The right solution, like Trout Software, can significantly ease this journey by offering user-friendly features and powerful capabilities. Unlock the value hidden in your logs, navigate your business more efficiently, and prepare for a safer, data-informed future 🚀