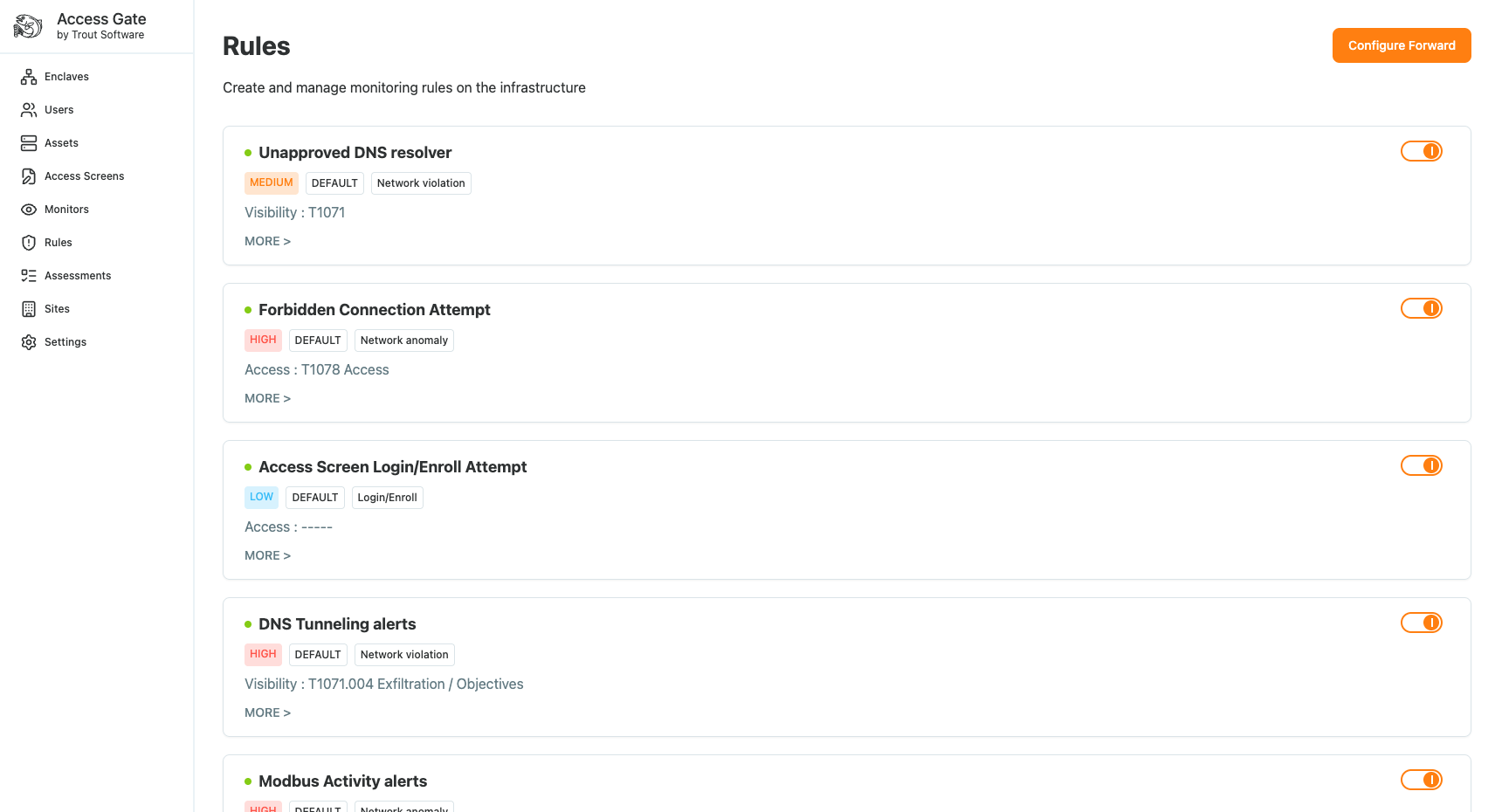
Access Gate generates detections based on behaviors and a set of rules that can be configured in Rules menu.
Syslog Destination
Access Gate sends events over syslog via TCP. Most SIEMs accept this out of the box: Splunk, Elastic, QRadar, and Sentinel (via its syslog connector) all work without custom integration.
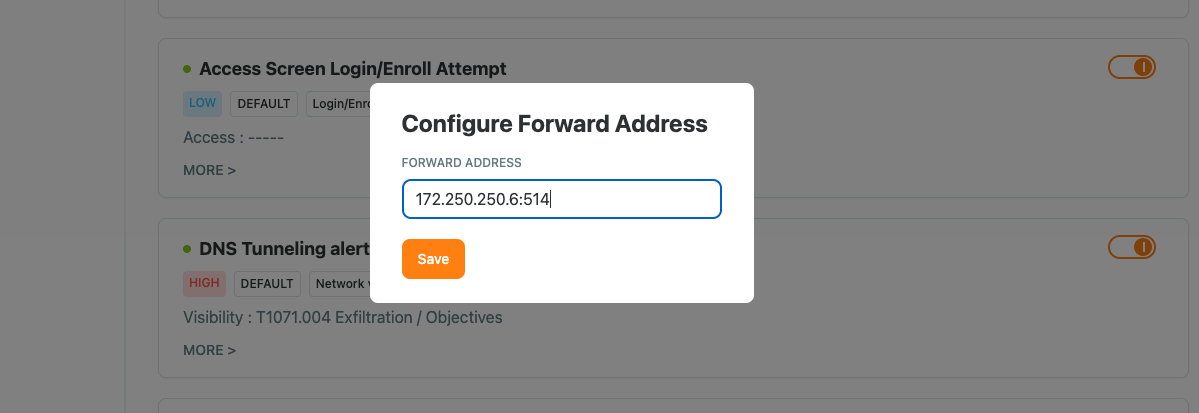
Configure a syslog destination
- Navigate to Rules → Configure Forward.
- Enter the hostname/IP, port (
514for example), and transport. - Pick which rules to send to this destination by ticking rules in the list
Related
- Log forwarding to Wazuh SIEM — Wazuh-side decoder and rules
- Log forwarding to Elastic SIEM — Logstash pipeline and Kibana setup
- Log forwarding to Splunk SIEM — TCP input, sourcetype, and alerts
- Detection and alerts — what populates the alert stream
- System logs and diagnostics information — on-box logs for troubleshooting
- Viewing enclave change history — what's in the audit stream