These are the standard deployment models for connecting Access Gate and structuring your network.
| Mode | Primary Purpose | Traffic Path | When to Use |
|---|---|---|---|
| Lollipop | On-site access control with zero rewiring | Adjacent to router; overlay-proxied | Default single-site deployment |
| Bastion | Controlled entry for remote users | VPN → Access Gate → assets | Remote operators, vendors, incident response |
| Multi-Site Mesh | Cross-site identity-based connectivity | Encrypted mesh between Access Gates | Multi-plant orgs, shared services, M&A |
Lollipop Mode (Standard Deployment)
Access Gate uses a lollipop topology rather than traditional inline deployment. The appliance connects to your network but doesn't sit in the physical traffic path.
Why Lollipop?
Traditional inline security devices create several problems:
- Single point of failure: Network goes down if device fails
- Performance bottleneck**:** All traffic limited by device throughput
- Complex deployment: Getting inline network changes right the first time is... challenging
- High risk: Misconfiguration can take entire network offline
Lollipop architecture solves these issues:
- Adjacent placement: Appliance sits beside network, not in the path
- Software-defined interception: Traffic redirected via DNS and routing
- Graceful degradation: Network functions normally if appliance offline
- Zero-touch deployment: No physical network changes required
How Traffic Flows
Without Access Gate (Underlay Network):Client → Asset
With Access Gate (Overlay Network Active): Client → Overlay IP → Route to Access Gate (Double NAT) → Underlay IP → Proxy to Asset
In the Access Gate scenario, it is important to note that the Client never access the Asset directly, but always through the proxy. The Access Gate initiate a second communication with the Asset (in red above).
This allows to deploy authentication, access control, monitoring... and all the good stuff.
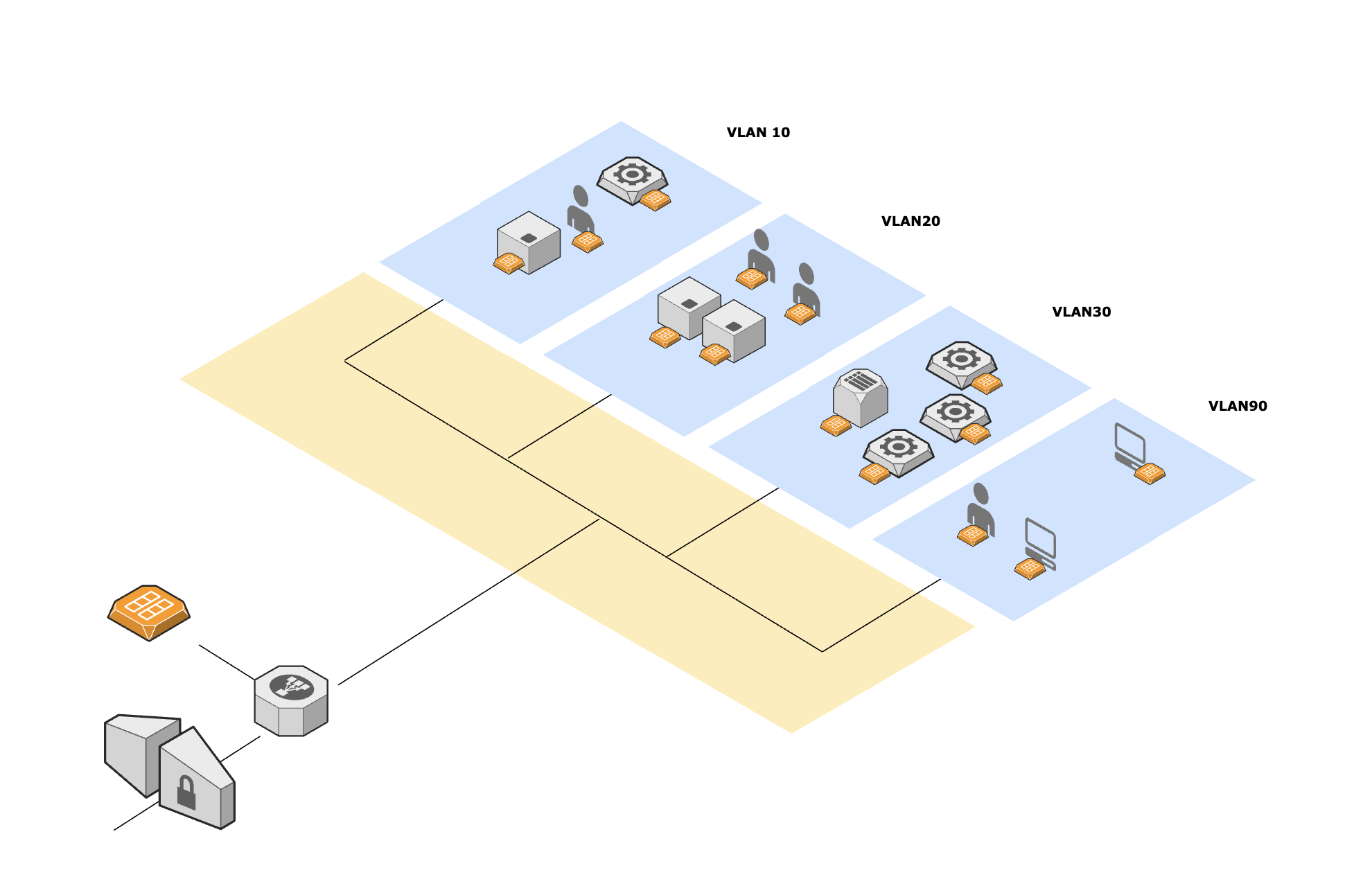
Lollipop deployment of an Access Gate
How it works
- Access Gate observes traffic via a netflow connection to the router
- Builds an overlay IP space (commonly 100.64.0.0/16) that maps protected services to proxy-enforced paths
- DNS resolves protected hostnames to overlay IP addresses
- Routing directs overlay traffic through Access Gate
- Assets remain on their original underlay network
Benefits
- No single point of failure in the traffic path
- No physical network changes required
- Simple to deploy and remove
- The network continues to operate normally if Access Gate is offline
Bastion Mode for Remote Access
What it is: Access Gate becomes the single controlled entry point for users coming from outside the site. Remote users connect via VPN (Tailscale/WireGuard) to Access Gate, and Access Gate brokers access to protected assets through its proxy.
Why this mode exists (the problem it solves): Remote access to OT / sensitive IT usually ends up as one of these patterns:
- Flat VPN into the LAN
- Jump box / RDP server
- Vendor remote tools
What Bastion Mode improves
- Least-privilege remote access
- Stronger boundary
- Auditability
- Operational safety
- Vendor access without permanent exposure
When to choose it
- You need remote access for operators, IT, vendors, or incident response.
- You want to avoid “VPN = inside the LAN.”
- You need consistent logs/evidence for NIS2/CMMC/NIST-style controls.
Access Gate acts as a VPN gateway, enabling remote users to securely reach on-site assets. The network flow looks like:
Remote Users → VPN (Tailscale / WireGuard) → Access Gate → Protected Assets
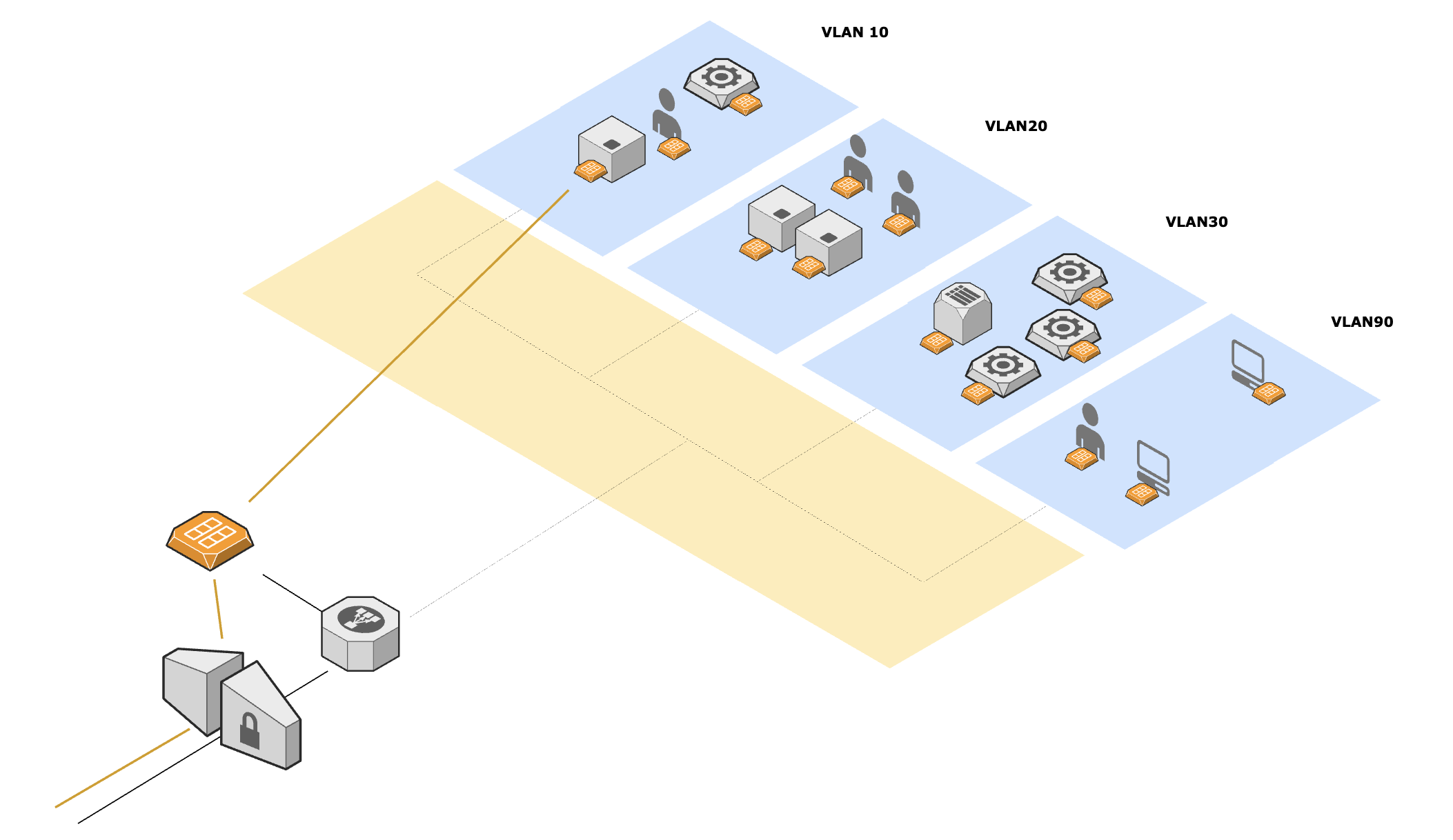
Bastion deployment of an Access Gate
Multi-Site Mesh
What it is: Multiple Access Gates form an encrypted mesh between sites. Each site keeps its local underlay unchanged, but selected assets/services become reachable across sites through controlled, identity-based policies.
Why this mode exists (the problem it solves) Organizations with multiple sites often end up with:
- Site-to-site VPNs that are flat
- Complex network engineering
- Inconsistent controls per site
What the mesh improves
- Zero-trust across sites (Alice on site A is able to access CNC on Site B)
- Standardized security posture
- Faster rollout
- Unified logging and documentation for auditors
Typical use cases
- Central engineering team needs controlled access to machines across plants.
- Shared services (historians, patch repositories, backup, monitoring) must be reachable securely.
- M&A / multi-entity environments where networks must remain separate but collaboration is required.
- You want “connectivity as policy” instead of “connectivity as routing.”
Multiple Access Gates interconnect over VPN to provide secure, site-to-site connectivity:
Site A Assets ← Access Gate A ←→ Access Gate B → Site B Assets
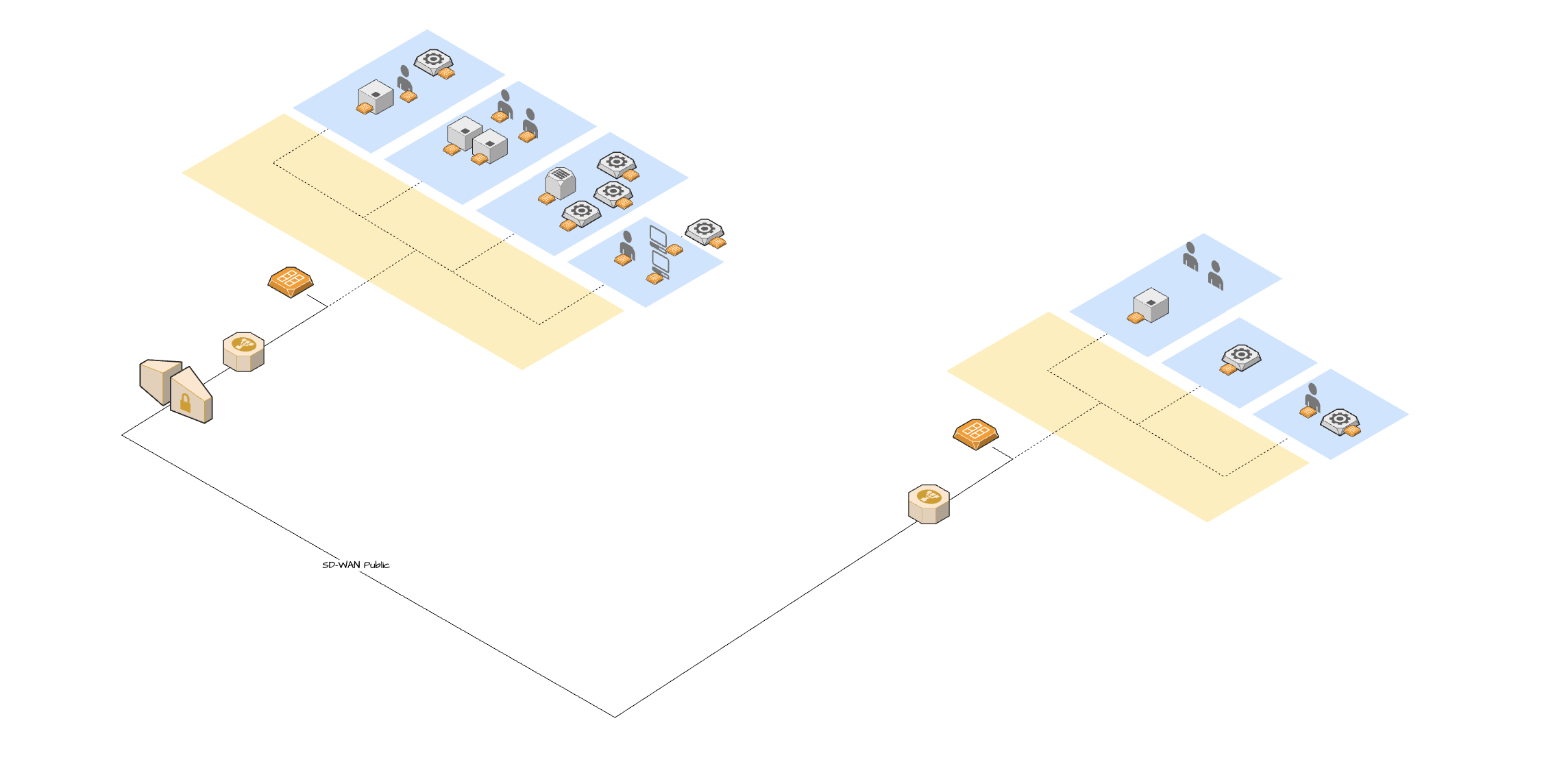
Access Gate implementation as a Multi-site Mesh
Requires: Site Mesh feature configuration