Voici les modèles de déploiement standard pour connecter Access Gate et structurer votre réseau.
| Mode | Objectif principal | Chemin du trafic | Quand l'utiliser |
|---|---|---|---|
| Lollipop | Contrôle d'accès sur site sans recâblage | Adjacent au routeur ; proxy en overlay | Déploiement par défaut sur site unique |
| Bastion | Point d'entrée contrôlé pour les utilisateurs distants | VPN → Access Gate → ressources | Opérateurs distants, prestataires, réponse à incident |
| Multi-Site Mesh | Connectivité inter-sites basée sur l'identité | Mesh chiffré entre Access Gates | Organisations multi-sites, services partagés, fusions-acquisitions |
Mode Lollipop (déploiement standard)
Access Gate utilise une topologie lollipop plutôt qu'un déploiement inline traditionnel. L'appliance se connecte à votre réseau sans se trouver dans le chemin physique du trafic.
Pourquoi le mode Lollipop ?
Les équipements de sécurité inline traditionnels posent plusieurs problèmes :
- Point de défaillance unique : le réseau tombe si l'équipement est hors service
- Goulot d'étranglement : tout le trafic est limité par le débit de l'équipement
- Déploiement complexe : réaliser correctement des modifications réseau inline du premier coup est... difficile
- Risque élevé : une mauvaise configuration peut mettre l'ensemble du réseau hors ligne
L'architecture lollipop résout ces problèmes :
- Placement adjacent : l'appliance se trouve à côté du réseau, pas dans le chemin
- Interception définie par logiciel : le trafic est redirigé via DNS et routage
- Dégradation gracieuse : le réseau fonctionne normalement si l'appliance est hors ligne
- Déploiement sans intervention physique : aucune modification réseau physique requise
Flux du trafic
Sans Access Gate (réseau underlay) : Client → Ressource
Avec Access Gate (réseau overlay actif) : Client → IP Overlay → Route vers Access Gate (Double NAT) → IP Underlay → Proxy vers la ressource
Dans le scénario Access Gate, le Client n'accède jamais directement à la ressource, mais toujours via le proxy. Access Gate initie une seconde communication avec la ressource (en rouge ci-dessus).
Cela permet de déployer l'authentification, le contrôle d'accès, la supervision… et tout ce qui va avec.
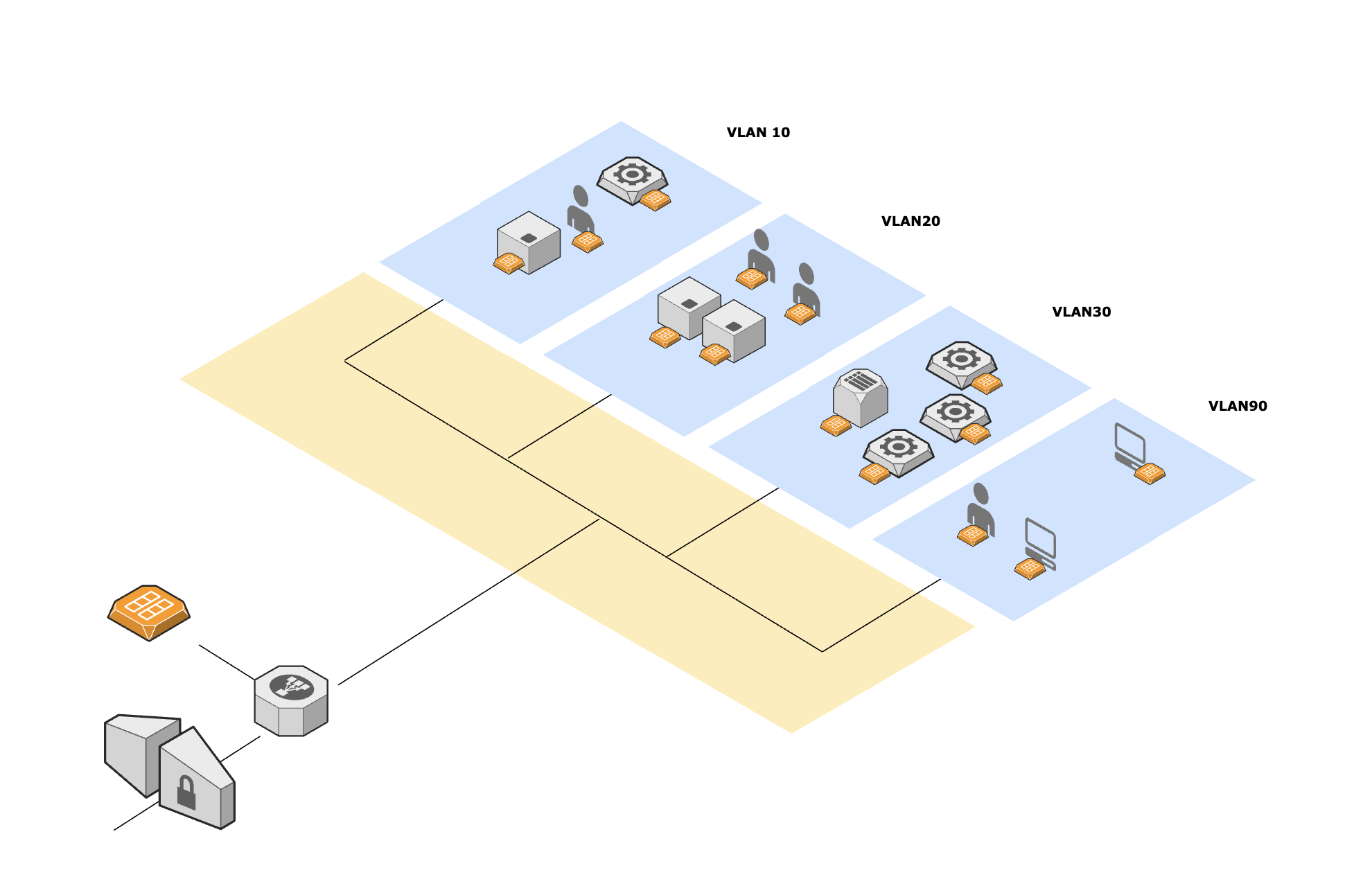
Déploiement Lollipop d'un Access Gate
Fonctionnement
- Access Gate observe le trafic via une connexion netflow vers le routeur
- Construit un espace d'adresses IP overlay (généralement
100.64.0.0/16) qui associe les services protégés à des chemins appliquant le proxy - Le DNS résout les noms d'hôtes protégés vers des adresses IP overlay
- Le routage dirige le trafic overlay à travers Access Gate
- Les ressources restent sur leur réseau underlay d'origine
Avantages
- Aucun point de défaillance unique dans le chemin du trafic
- Aucune modification réseau physique requise
- Déploiement et retrait simples
- Le réseau continue de fonctionner normalement si Access Gate est hors ligne
Mode Bastion pour l'accès distant
Ce que c'est : Access Gate devient le point d'entrée unique et contrôlé pour les utilisateurs venant de l'extérieur du site. Les utilisateurs distants se connectent via VPN (Tailscale/WireGuard) à Access Gate, qui gère l'accès aux ressources protégées via son proxy.
Pourquoi ce mode existe (le problème qu'il résout) : L'accès distant aux environnements OT / IT sensibles se retrouve généralement dans l'un de ces schémas :
- VPN plat vers le LAN
- Jump box / serveur RDP
- Outils d'accès distant des prestataires
Ce que le mode Bastion améliore
- Accès distant selon le principe du moindre privilège
- Périmètre renforcé
- Auditabilité
- Sécurité opérationnelle
- Accès prestataires sans exposition permanente
Quand le choisir
- Vous avez besoin d'un accès distant pour des opérateurs, des équipes IT, des prestataires ou une réponse à incident.
- Vous souhaitez éviter que « VPN = accès au LAN ».
- Vous avez besoin de journaux et de preuves cohérents pour les contrôles de type NIS2/CMMC/NIST.
Access Gate joue le rôle de passerelle VPN, permettant aux utilisateurs distants d'atteindre de manière sécurisée les ressources sur site. Le flux réseau est le suivant :
Utilisateurs distants → VPN (Tailscale / WireGuard) → Access Gate → Ressources protégées
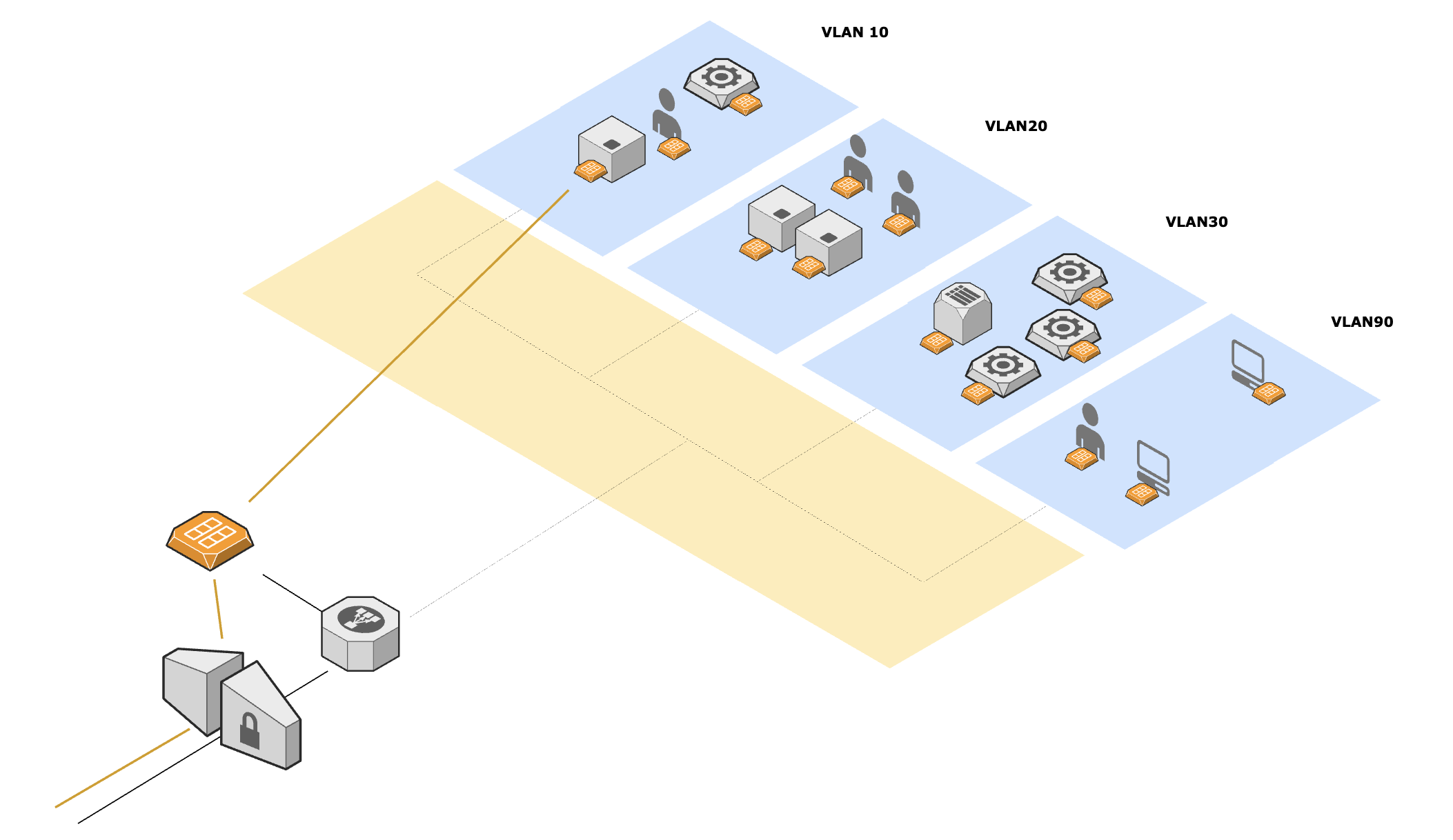
Déploiement Bastion d'un Access Gate
Multi-Site Mesh
Ce que c'est : Plusieurs Access Gates forment un mesh chiffré entre les sites. Chaque site conserve son réseau underlay local inchangé, mais certaines ressources et certains services deviennent accessibles entre sites via des politiques contrôlées et basées sur l'identité.
Pourquoi ce mode existe (le problème qu'il résout) : Les organisations multi-sites se retrouvent souvent avec :
- Des VPN site à site à plat
- Une ingénierie réseau complexe
- Des contrôles hétérogènes selon les sites
Ce que le mesh améliore
- Zero Trust entre les sites (Alice sur le site A peut accéder à une CNC sur le site B)
- Posture de sécurité standardisée
- Déploiement accéléré
- Journalisation unifiée et documentation pour les auditeurs
Cas d'usage typiques
- Une équipe d'ingénierie centrale a besoin d'un accès contrôlé aux machines de plusieurs usines.
- Des services partagés (historians, dépôts de correctifs, sauvegarde, supervision) doivent être accessibles de manière sécurisée.
- Environnements issus de fusions-acquisitions ou multi-entités où les réseaux doivent rester séparés tout en permettant la collaboration.
- Vous souhaitez une « connectivité comme politique » plutôt qu'une « connectivité comme routage ».
Plusieurs Access Gates s'interconnectent via VPN pour fournir une connectivité sécurisée entre sites :
Ressources site A ← Access Gate A ←→ Access Gate B → Ressources site B
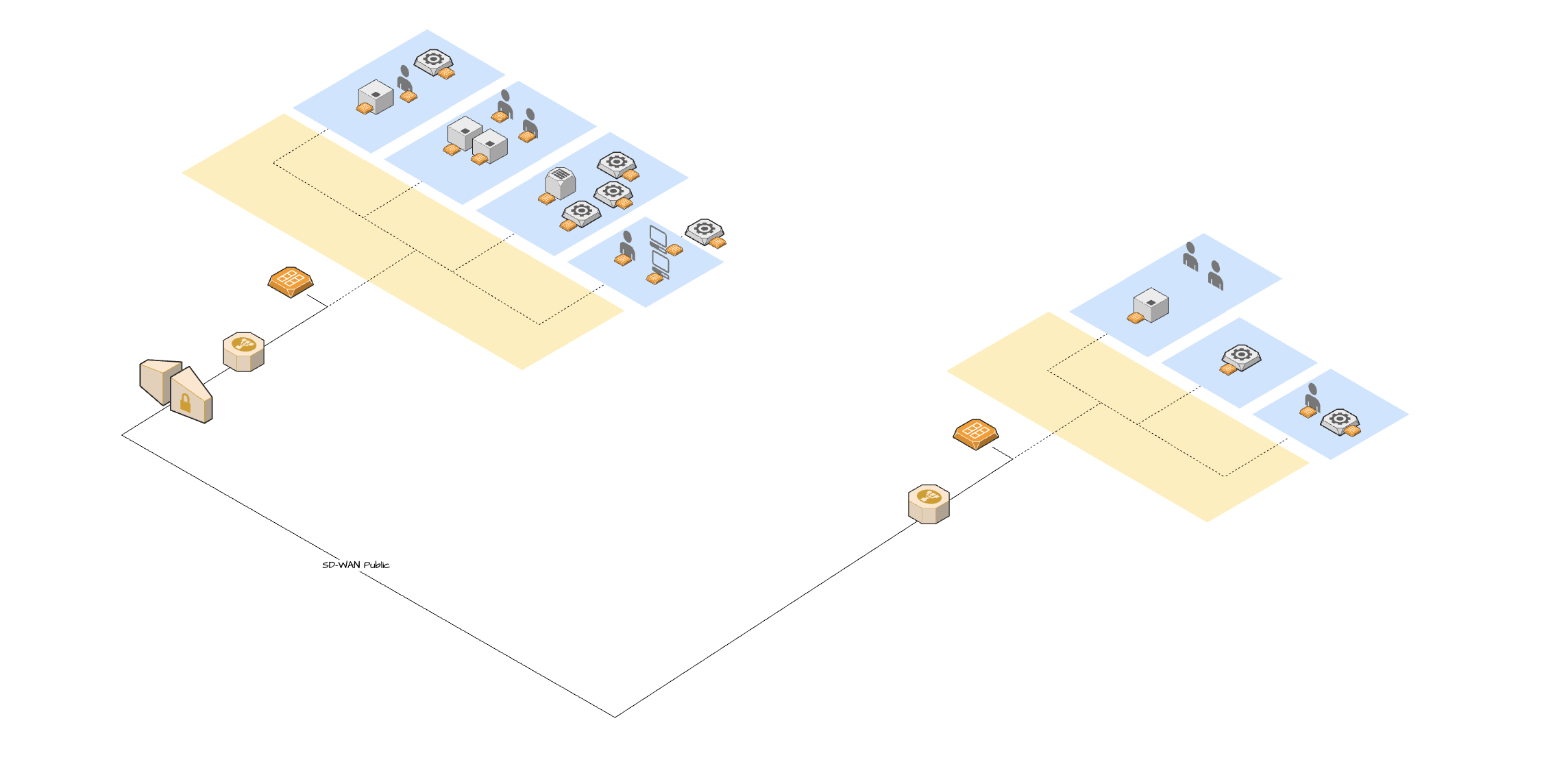
Implémentation d'Access Gate en Multi-site Mesh
Prérequis : configuration de la fonctionnalité Site Mesh